What Does a Reverse Engineer Do in Cybersecurity



Reverse engineering is like solving a digital puzzle, where each piece of software holds secrets waiting to be unraveled. For cybersecurity professionals, reverse engineering is a powerful tool for understanding software vulnerabilities, analyzing malware, and fortifying digital defenses. This article dives into the fascinating world of reverse engineering in cybersecurity, illuminating the role of reverse engineers and the critical impact they have on protecting our digital landscape.
Whether you’re a cybersecurity enthusiast, a student dreaming of a career in the field, or an IT manager exploring advanced security measures, you’ll walk away with a clearer understanding of reverse engineering and why it’s indispensable for cyber defense.
What is reverse engineering in cybersecurity?
Simply put, reverse engineering is the process of deconstructing software or systems to uncover how they work. Think of it as "unscrambling the code" to identify vulnerabilities, threats, or weaknesses in the architecture.
Within the realm of cybersecurity, reverse engineering is most frequently applied to:
Malware analysis: Breaking apart malicious software to understand its behavior, origin, and impact.
Vulnerability discovery: Identifying weak spots in software that attackers could exploit.
Protocol analysis: Studying proprietary or obscure communication protocols.
Intellectual property enforcement: Analyzing software for misuse or breaches of licensing agreements.
Unlike ethical hacking, which proactively tests a system's defenses, reverse engineering works by examining a system or software post-development to understand its inner workings, even without access to its source code.
What does a reverse engineer do?
Reverse engineers are the detectives of the cybersecurity world. They analyze software, uncover vulnerabilities, and provide insights that drive defense strategies. Here’s a closer look at their typical day-to-day responsibilities:
Analyze Malware
Reverse engineers dissect malicious code to determine its payload, evasion techniques, and command-and-control (C2) communication.
Identify Software Vulnerabilities
By deconstructing executables (e.g., EXE or DLL files), reverse engineers uncover exploitable vulnerabilities that could endanger systems.
Develop Detection Signatures
They create rules for tools like YARA or antivirus software to identify similar threats in the future.
Support Threat Intelligence Teams
Reverse engineers provide critical indicators of compromise (IOCs) to bolster an organization's incident response efforts.
Decrypt Obfuscated Code
They decrypt or deobfuscate code to reveal hidden functionalities malicious actors try to conceal.
Contribute to Software Forensics
Reverse engineers play an essential role in intellectual property disputes, ensuring software is used ethically and legally.
Essentially, they serve as the protectors who unravel cyber threats from the ground up, translating complex code into actionable insights.
Key responsibilities of a reverse engineer
Reverse engineers' expertise spans both technical and strategic dimensions. Here’s what their job roles look like in detail:
Code Analysis: Conduct static and dynamic analysis of binaries to study structure and behavior.
Tool Utilization: Use hex editors, disassemblers (IDA Pro, Ghidra), and debuggers (x64dbg, WinDbg) for in-depth analysis.
File Format Inspection: Dissect binary formats like EXE, ELF, and DLL to understand the architecture.
Documentation: Create detailed reports and communicate findings to internal security teams and external stakeholders.
Vulnerability Research: Contribute to vulnerability databases (such as CVE disclosures) for safer, more robust software ecosystems.
Tools and techniques used by reverse engineers
The work of reverse engineering would be near impossible without specialized tools. Here’s a breakdown of the essential ones:
Disassemblers: IDA Pro, Ghidra, Radare2
Breaks down machine code into human-readable assembly code.
Debuggers: x64dbg, WinDbg, OllyDbg
Continues program execution line-by-line to observe its behavior.
Sandboxes: Cuckoo, Any.Run
Executes malicious software safely in a controlled environment for behavior analysis.
Decompilers: Hex-Rays, JEB
Converts machine code back to high-level code.
Network Analyzers: Wireshark, Fiddler
Monitors and inspects network traffic for malicious communication.
Scripting: Python scripting tools like Binary Ninja plugins allow for tailored analysis workflows.
By using a combination of these tools, reverse engineers deconstruct the most complex malicious software to help secure organizations against cyber threats.
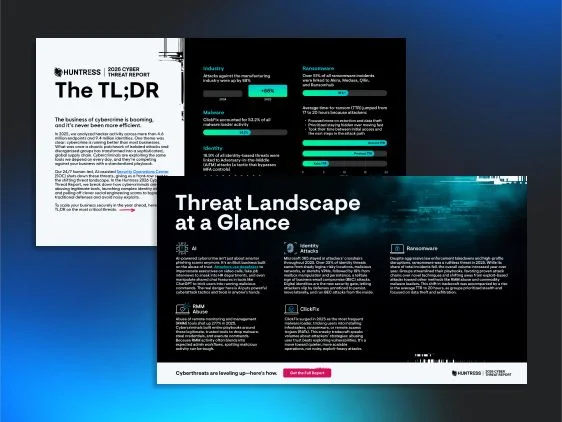
2026 Cyber Threat Report: The TL;DR
Sophisticated attackers use reverse engineering to analyze defenses and find gaps before they strike, making adversarial tradecraft knowledge essential for modern defenders, so download the Huntress 2026 Cyber Threat Report TL;DR to get frontline intelligence on the threats and techniques our SOC is seeing most in the wild.

Steps in the reverse engineering process
Reverse engineers typically follow a structured methodology to systematically analyze and understand software. Here’s a step-by-step breakdown:
1. Sample Acquisition
Obtain a software sample or malware specimen.
2. Environment Setup
Set up an isolated, secure environment such as a virtual machine (VM) to safely conduct analysis.
3. Static Analysis
Extract metadata, embedded strings, and file structures without running the file.
4. Dynamic Analysis
Run the file in a sandbox to monitor its behavior in real time.
5. Debugging
Use debugging tools to step through the program's execution and uncover hidden layers.
6. Documentation
Record detailed findings, including malware payloads, vulnerabilities, and strategies for mitigation.
7. Mitigation Strategies
Develop solutions such as patches, detection signatures, or countermeasures based on documented findings.
This process forms the backbone of threat research and response in cybersecurity.
Why reverse engineering matters in cyber defense
Reverse engineering contributes directly to the safety and efficiency of enterprise systems and national infrastructure. Its real-world applications include:
Analyzing Advanced Persistent Threats (APTs): Helps defend against sophisticated long-term cyberattacks.
Decrypting Ransomware: Supports the development of decryption tools to recover locked systems.
Uncovering Zero-Day Vulnerabilities: Identifies unknown vulnerabilities before attackers can exploit them.
Investigating Supply Chain Attacks: Tracks malicious code injected into third-party software.
Forensic Examination: Plays a pivotal role in post-breach analysis and legal proceedings.
Without reverse engineers, cybersecurity would lack its crucial backbone of thorough analysis and strategic response.
Building a career in reverse engineering
Are you considering a career in reverse engineering? Here’s what it takes to succeed:
Skills You Need:
-
Proficiency in assembly language (x86/x64 and ARM).
-
Knowledge of OS internals like Linux and Windows.
-
Familiarity with malware obfuscation and unpacking techniques.
Certifications to Pursue:
-
GIAC Reverse Engineering Malware (GREM)
-
Offensive Security Certified Expert (OSCE3)
Recommended Tools for Beginners:
-
Ghidra
-
x64dbg
-
Cutter
Community Resources:
Engage with forums, Capture-the-Flag (CTF) challenges, and online courses to gain hands-on experience.
Start small, stay curious, and remember that becoming skilled in reverse engineering is as much about creativity as it is about technical know-how.
Empower cyber defense with reverse engineering
Reverse engineers are the unsung heroes of cybersecurity. Their work not only protects enterprises from emerging threats but also bolsters innovation in areas like malware research and vulnerability detection.
If you’re ready to tackle the intricate puzzles of reverse engineering, now is the perfect time to start. Whether you’re passionate about security or embarking on a new tech career, this field promises endless learning, impactful challenges, and a way to truly make a difference.
Stay curious, stay secure, and take the first step into the fascinating world of reverse engineering.
Huntress Annual Capture the Flag Event
Every October during Cybersecurity Awareness Month, Huntress hosts a month-long Capture the Flag (CTF) competition. It's a challenge designed for (mostly) everyone, from beginners dipping their toes into cybersecurity to seasoned experts looking to flex their skills.


FAQs about reverse engineering in cybersecurity
Reverse engineering focuses on deconstructing software or malware to understand its components, while ethical hacking simulates real-world attacks on systems to proactively identify weaknesses.
It’s legal when conducted with proper authorization or for legitimate purposes like research, malware analysis, or strengthening security. However, it can violate terms of service or intellectual property laws without consent.
It requires time and dedication. Mastery involves learning low-level programming, advanced debugging, and gaining hands-on experience with reverse engineering tools.



Additional Resources
- Read more about What is a decompiler for cybersecurityLearn what decompilers are, how they work, and their role in malware analysis. Understand why decompilers are essential for cybersecurity professionals
- Read more about Network Security Engineers: Business Cybersecurity ImpactNetwork Security Engineers: Business Cybersecurity ImpactLearn what network security engineers do, how critical this role is in business security and what it takes to get started in this high-demand role.
- Read more about What Does a Security Engineer Do? Roles & SkillsWhat Does a Security Engineer Do? Roles & SkillsLearn what security engineers do, their key responsibilities, and career paths. Learn how they safeguard IT infrastructure and protect organizations
- Read more about What Does a Cybersecurity Researcher Do?What Does a Cybersecurity Researcher Do?Learn what cybersecurity researchers do by exploring tasks, required skills, and career paths in this essential cybersecurity role.
- Read more about What is Offensive Security? | Cybersecurity 101What is Offensive Security? | Cybersecurity 101Learn how offensive security helps organizations find vulnerabilities before attackers do. Discover penetration testing, red teaming, and proactive defense strategies.
- Read more about What Does a Cybersecurity Manager Do?What Does a Cybersecurity Manager Do?Learn about cybersecurity manager roles, responsibilities, skills, and career outlook. Discover how these leaders protect organizations from cyber threats.
- Read more about What is a Malware Packer? Detection & Analysis GuideWhat is a Malware Packer? Detection & Analysis GuideLearn how malware packers disguise malicious code to evade security tools. Discover detection techniques and analysis methods used by cybersecurity pros.
- Read more about What Does a Bug Bounty Hunter Do in Cybersecurity?What Does a Bug Bounty Hunter Do in Cybersecurity?Explore the role of bug bounty hunters in cybersecurity. Learn how ethical hackers find and report security flaws to protect organizations.
- Read more about What is Malware Analysis?What is Malware Analysis?Discover the basics of malware analysis, its types, and importance in cybersecurity. Learn how professionals analyze malware to protect systems effectively.


Protect What Matters