In the past year, hackers have started trading in the proverbial black hoodie and are opting instead for a “cloak of invisibility.” The result? Cybercriminals are hiding—often in plain sight—and moving covertly in systems before unleashing havoc.
In the Huntress 2024 Cyber Threat Report, our teams cover how adversaries have begun to camouflage themselves behind legitimate tools. Based upon data collected from millions of endpoints and user entities under our watch, this report documents some of the most unsettling trends, patterns, and tactics the Huntress team observed throughout 2023. Let’s get into it.
Pulling the Ultimate Disappearing Act
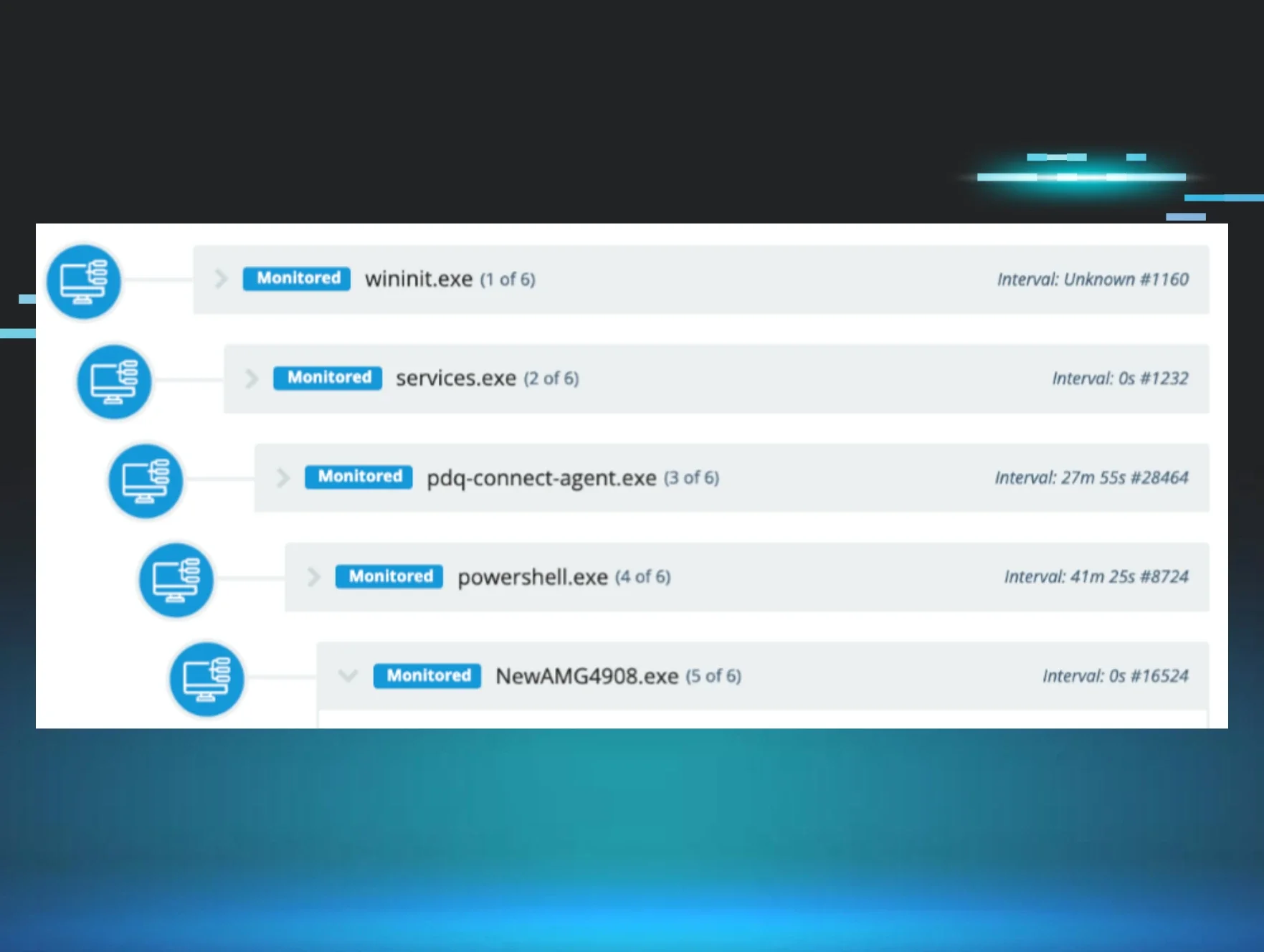
Huntress has long observed the shady behavior of threat actors—often blending into legitimate scripts, processes, or general network noise. But this past year, we noticed something interesting: hackers are weaponizing legitimate tools to pull their "disappearing act."
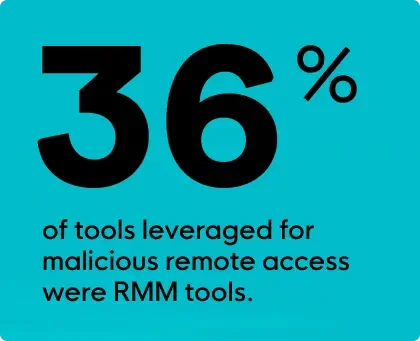
This goes beyond a “Trojan Horse” scenario. This is more like a sinister infiltration of programs and tools you know and trust—things like using remote monitoring and management (RMM) tools to gain access to systems you never even knew were vulnerable. It’s a pattern Huntress observed throughout 2023, with remote access abuse occurring on popular tools like ScreenConnect and Atera. In fact, 36% of tools leveraged for malicious remote access were RMM tools that many organizations rely on for managing their infrastructure and devices.
It appears that hackers don’t need to reinvent the wheel. Instead, they can use known platforms like cloud storage systems to infiltrate and move covertly towards larger, more damaging, and, of course, more lucrative exploits. In 2023, nearly 80% of cloud storage misuse incidents involved OneDrive. This is just one example of ways in which cybercriminals leveraged services like OneDrive, Google, or Dropbox to distribute malware or exfiltrate the data that helps them make money.
What to Expect: Hackers Working Smarter, Not Harder
Cybercriminals—like most of us—have had an interesting couple of years. The work-from-home shift of the pandemic forced more organizations to finally confront their cybersecurity vulnerabilities. More companies are addressing their sorely lacking endpoint security. Though, let’s be clear: everyone could stand to improve.
Threat actors, however, are a creative bunch. They never miss an opportunity for new shenanigans.
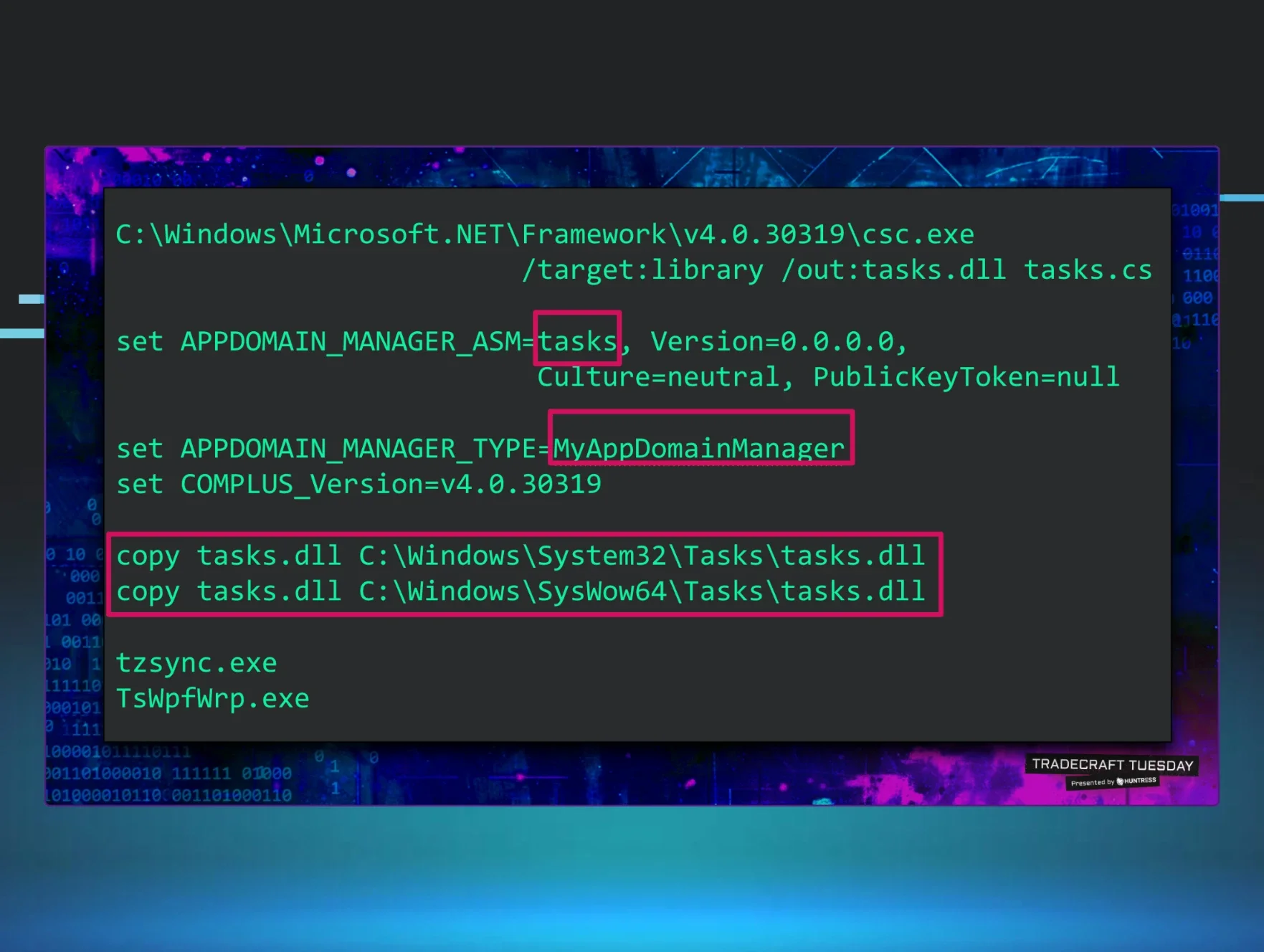
That’s why weaponizing the tools organizations already use is one of the preferred methods attackers are using to gain remote access and control. These off-the-shelf tools are often created or implemented with the very vulnerabilities hackers depend on for successful exploits. Why bother creating new tools or malware of their own when these creative attackers can work smarter, not harder, and just use the tools businesses are already paying to use?
From RMM to OneDrive, these tools add value and function to everyday business operations. But in 2023, we saw that they do carry a risk level of exploitation. Gone are the days when hackers needed to evade detection. Today, they can cloak themselves in ways you may never see coming.