What is Mimikatz?
Written by: Brenda Buckman
Published: 9/5/2025



Frequently Asked Questions (FAQs)
Mimikatz is like the Swiss Army knife of post-exploitation tools—but for bad guys. It’s famous for extracting plaintext credentials, password hashes, Kerberos tickets, and other authentication goodies from Windows systems. Originally built for research, it’s now a go-to tool for both penetration testers and attackers. Think red teaming, privilege escalation, and lateral movement.
Short version? Mimikatz digs into the LSASS (Local Security Authority Subsystem Service) process in memory, pulling out sensitive authentication data. If someone has admin or SYSTEM-level access, they can grab:
Plaintext passwords (only if WDigest is enabled)
NTLM hashes
Kerberos tickets
With these in hand, attackers can kick off pass-the-hash or pass-the-ticket attacks to cause even more trouble.
Here’s the deal: Mimikatz is completely legal when you’ve got permission to use it. Penetration tests, red team exercises, or security research? You’re good. But using it on systems without authorization? Hard pass. That’s illegal and puts you on the wrong side of cybersecurity laws.
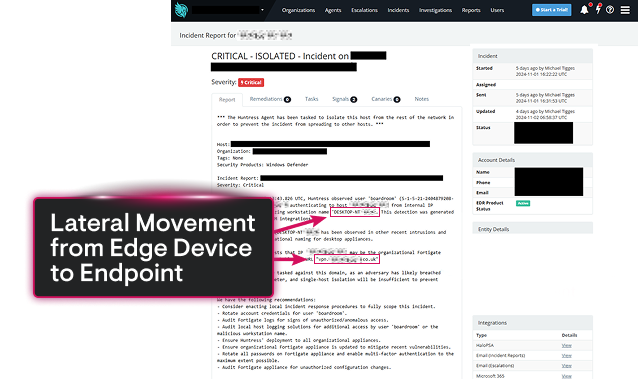
Once attackers are inside, Mimikatz helps them pivot and escalate privileges. Here’s the playbook:
Grab NTLM hashes to log into other devices without passwords.
Forge Kerberos tickets (like golden tickets) to impersonate users.
Perform DC Sync attacks to snatch password data straight from Domain Controllers.
Basically, they’re unlocking all the doors to sensitive systems, maintaining persistence, and escalating their access.
Spotting Mimikatz can save you a world of pain. Here’s how you can catch it in action:
Use EDR or XDR tools to monitor for LSASS memory tampering.
Flag known Mimikatz command-line arguments.
Look for PowerShell or scripting behaviors tied to credential dumping.
Set up Sysmon rules to catch unusual access patterns.
Bonus tip? Watch for weird Kerberos activity or replication anomalies in your domain controllers.
They’re like cousins in the credential-stealing family:
Pass-the-Hash (PtH): Use an NTLM hash to log into systems, no password needed.
Pass-the-Ticket (PtT): Use a swiped Kerberos ticket (TGT or TGS) to pretend you’re a legit user.
Both bypass passwords, but PtH exploits NTLM authentication, while PtT focuses on Kerberos.
Short answer? Yes—but it takes effort. Here’s your battle plan:
Enable Credential Guard to block LSASS access.
Turn on RunAsPPL to give LSASS extra protection.
Disable WDigest unless you absolutely need it.
Follow strict least privilege principles and keep an eye on admin activity.
While Mimikatz can’t always be outright stopped, these steps make it far harder for attackers to succeed. Keep it tight, stay vigilant.