Huntress vs. Sophos
Sophos gives you a broad security ecosystem for a price. With Huntress, you get a fully managed security platform without the tiers. Learn why businesses choose Huntress over other threat monitoring platforms for extensive coverage, deep transparency, managed simplicity, and straightforward pricing.
-
Managed endpoint and identity protection, log correlation, and security awareness training—backed by a 24/7 human-led, AI-centric SOC that investigates and responds before you even see an alert.
-
Human-led outcomes with less than 1% false positives for Managed EDR and <5% for Managed ITDR.
-
Built for lean IT teams, not giant SOCs—Huntress is optimized for <1% false positives and industry‑leading response times (minutes, not hours), so smaller teams actually get outcomes instead of drowning in tuning and noise.
-
Simple predictable pricing- volume-based price per tool. No tiers. No gated features.
Enterprise-grade protection built for businesses like yours.

What Purpose-Built Security For SMBs Looks Like


SOC-led incident response across EDR, ITDR, and SIEM. Analyst-validated, actionable alerts with virtually no false positives.

Two MDR tiers with additional purchase. ITDR and SIEM add-ons are required for full coverage.


~8-minute MTTR for EDR” and “3-minute MTTR for ITDR.” I’d say “around 3 minutes” vs “under 3 minutes.

Sophos advertises sub-30-minute initial response, but does not publish MTTR.


Lightweight EDR with advanced behavioral detection, <1% false positive rate, industry-leading MTTR, and 24/7 SOC monitoring. Works alongside your existing AV, including Microsoft Defender, SentinelOne, and others—no migration required.

Intercept X is a full endpoint replacement, requiring rip-and-replace or redundant tooling. Strong detection, but some users note that agent weight degrades performance in older hardware.


Native Managed ITDR for Microsoft 365 (including Entra ID) and Google Workspace, with support for hybrid Entra-backed environmentsDetects account takeover, privilege escalation, and MFA bypass. SOC responds in under three minutes.

ITDR is available as an add-on to MDR or XDR. Covers IDs, dark web credential monitoring, and dozens of posture checks. No published MTTR. Managed services require MDR.


Fully managed SIEM built natively into the Huntress platform. Smart Filtering cuts alert noise. Per-source pricing with no per-GB overages. Includes 30-day hot storage and 1-year cold storage.

Sophos often relies on separate SIEM/log platforms and add-on integrations for full log correlation, which can add another portal and cost layer.


Fully managed SAT with simulated phishing, just-in-time lessons, compliance modules, and custom content creation tools.

Phish Threat bundled with Sophos Email. Less managed than Huntress—requires more manual campaign setup. Less integration with endpoint/identity data for just-in-time training.


Every incident triggers a human-written report detailing initial access through remediation. Built for audits, QBRs, and boards.

Higher-tier MDR Complete includes root cause reports and a dedicated IR Lead during incidents.


Speak to a SOC analyst 24/7—no extra cost.

MDR Essentials offers chatbot and helpdesk ticket support. Technical Account Manager (TAM) is an add-on. MDR Complete includes IR Lead during incidents only.


One simple, volume-based price per product. No feature tiers to unlock full capabilities or response.

Tiered pricing model. Access to full capabilities requires higher-tier commitments and add-ons (third-party integration, TAM, extended retention, etc.). Costs compound quickly.


Enterprise-grade security without the complexity
Get security outcomes, not just a platform.

Enterprise-grade tools, backed by human expertise

Human expertise is built in

Fully managed, 24/7 coverage across your environment

Response speed and automation capabilities compared
In an active attack, quick detection and containment are crucial for minimizing the blast radius. Here's how the platforms compare on response:
-
Huntress: ~8-minute mean time to respond to endpoint incidents. Under 3 minutes on identity threats. The SOC acts first by isolating hosts, killing malicious processes, disabling compromised accounts, and revoking sessions, then notifies you with a clear remediation summary and any remaining action items.
-
Sophos MDR: Has a 24/7 SOC with active response capabilities. However, response time can be significantly longer. Sophos targets an initial response within 30 minutes. Response automation depends on response mode configuration and may require internal team action. Sophos tools are self-managed without MDR purchase.
Managed security operations differences for SMBs
For small and mid-sized businesses and the MSPs that serve them, adding security without friction is essential.
Huntress was built so IT generalists can run it day to day without a dedicated internal security team. Huntress is up and running in under 30 minutes with a lightweight agent that won’t bog down operations. The SOC is your force multiplier, taking on alert triage, investigation, and the bulk of response. You see only a small number of high-fidelity incidents with clear next steps, sparing your team from alert fatigue and helping ensure threats aren’t missed.
Sophos MDR offers similar SOC capabilities, but the ecosystem tends to be more enterprise-focused. A more complex console with a breadth of products to manage and more decisions to make. While Sophos has simplified its SKUs by folding in separate add-ons, this can lock customers into higher-tier purchases.
If you want a managed platform that already covers endpoint, identity, SIEM, and SAT today and in one portal at one predictable price, Huntress is the more complete choice.
Learn more about how Huntress is built for MSPs.
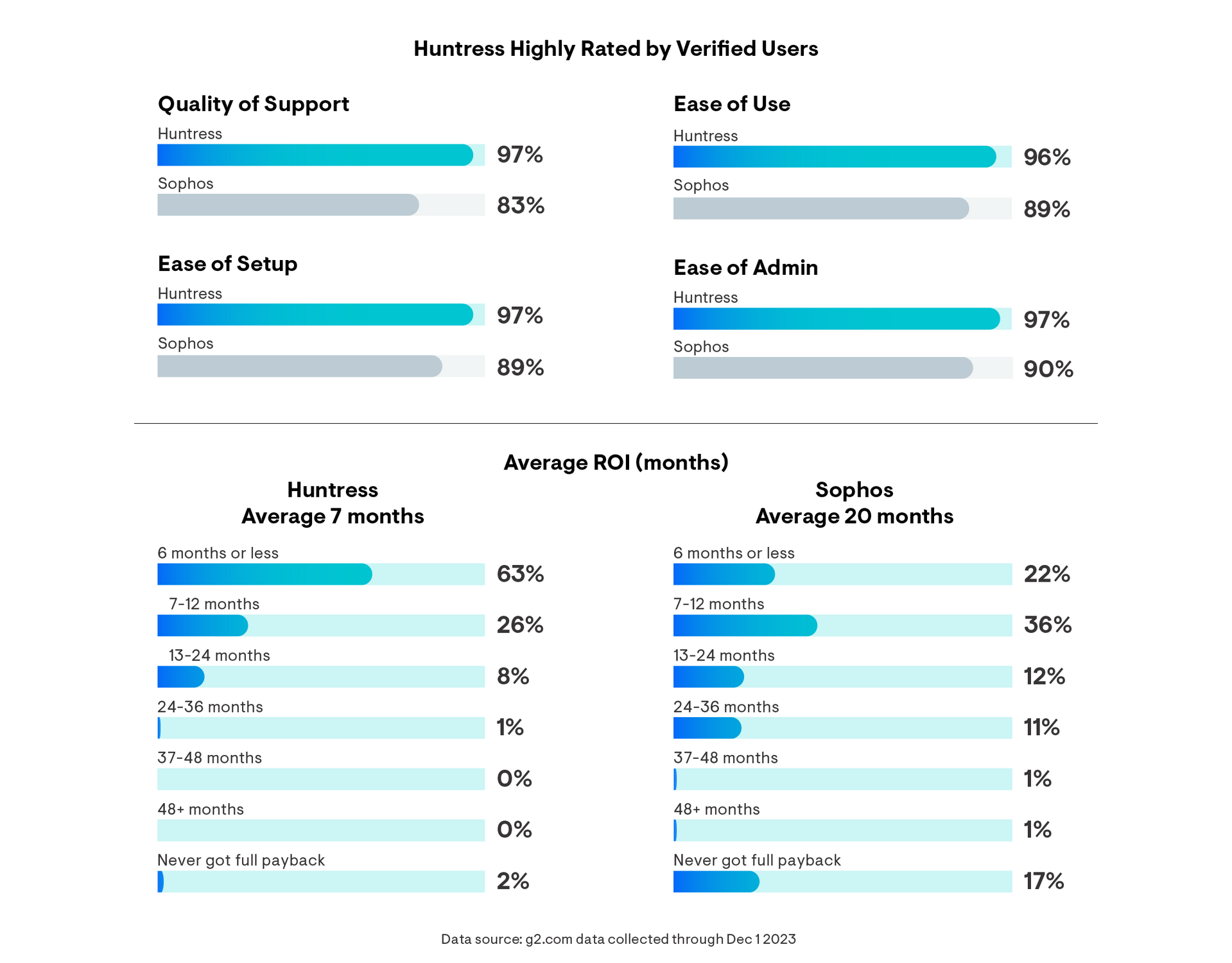
Deployment, maintenance, and customer support comparison
Huntress simplifies deployment, handles maintenance, and delivers the industry’s best customer support to ensure your security platform is frictionless from day one.
Getting started
Huntress starts protecting your systems in under 20 minutes. Deploy agents via RMM, Intune, or GPO. There’s no need for professional services, but onboarding support is always there for you at no charge. Our lightweight agents work seamlessly with your current stack. Using Microsoft Defender AV? We’ll manage it for you, no additional cost.
Self-onboarding with Sophos is possible, but more complex. Because the Breach Protection Warranty requires a “100% Health Check Score,” misconfigurations may also invalidate the breach warranty. While Sophos offers MDR for Microsoft Defender, implementing its endpoint agent, Intercept X Advanced, means a rip-and-replace migration. You must also choose whether to keep your current firewall and NDR by paying for additional integrations or buy into the Sophos ecosystem. Sophos offers paid professional services and operational support.
Ongoing maintenance
With Huntress, the SOC, detection engineering, and Smart Filtering continuously tune the platform for you, with no in-house security engineer or specialist required. Updates ship on an ongoing, high-frequency cadence.
While Sophos has consolidated much of its agent footprint, additional components or integrations may still be required. Some customers have noted performance issues on underpowered hardware, while others say automatic updates sometimes require manual intervention.
Support and transparency
Huntress delivers human-written incident reports with every confirmed threat. Every signal investigated is closed with a written reason (benign, business-accepted risk, or pen test), so you always know why an alert was or wasn't raised. The SOC’s human experts are there 24/7 to answer your questions—just pick up the phone.
Sophos offers tiered support. To speak with a human advisor, you have to pay for another add-on. Higher-tier MDR Complete includes an incident response lead during incidents, but doesn’t include day-to-day support.
Pricing and value analysis
Both platforms use volume-based pricing, but the structure differs in ways that matter at scale.
Huntress: Simple, per-product pricing based on volume. EDR covers endpoints, ITDR monitors identities, SIEM correlates logs from across the environment, and SAT provides ongoing training. All products have full capabilities and come fully managed by default—no exceptions, no surprise overages.
Sophos MDR: Sophos MDR is priced by quote. To achieve similar cross-layer protection to the full Huntress platform, you would need MDR Complete + ITDR add-on + third-party integration packs (if using non-Sophos sources) + extended retention (if >90 days needed) + TAM (if human advisory required). Phish Threat is now bundled into Sophos Email.
For MSPs building a per-seat or per-client pricing model, Huntress's flat, predictable structure is easier to bundle and margin-protect. You pay for what you use, and every product delivers full functionality from day on
Unmasking Cyber Villians
Testimonials


The Huntress Managed Security Platform






Huntress vs. Sophos FAQs
You can run Huntress alongside Sophos or move fully to a Huntress-centric stack over time. Our Managed EDR includes 24/7 SOC coverage by default, so you don't need a separate MDR SKU to get round-the-clock monitoring and response—something Sophos requires as an additional purchase.
Many teams use an overlap period to validate Huntress detections and workflows, then phase out Sophos endpoint and MDR licenses once they're confident that Huntress Managed EDR—often paired with Microsoft Defender—is covering their needs.
Yes. Our agent is designed to run alongside other AV/EDR tools, including Sophos. Follow standard best practices and allow-list Huntress in your security stack—we provide documented exclusion guidance for Sophos and other common AV/EDR tools to avoid CPU spikes, slowdowns, or blocked installs.
Most partners deploy Huntress on top of their existing Sophos estate first, add the recommended exclusions, and then decide whether to move toward a Defender-plus-Huntress stack from there.
Our agent is intentionally lightweight and built to run without disrupting day-to-day operations, even on older hardware. It works alongside your existing AV—including Microsoft Defender, SentinelOne, and others—so there's no rip-and-replace migration required.
Sophos Intercept X is a full endpoint replacement, which means either migrating away from your current AV or carrying redundant tooling. Some users have reported performance slowdowns after installation, particularly on older hardware.
Huntress uses simple, volume-based per-product pricing. Every product—EDR, ITDR, SIEM, and SAT—is fully managed and fully featured by default. No tiers to unlock, no surprise overages, and SOC access is included at every level.
Sophos MDR is priced by quote, and reaching the same cross-layer coverage as Huntress typically means combining multiple Sophos SKUs for endpoints, servers, MDR, and other add-ons. For MSPs building per-seat or per-client pricing models, Huntress's flat structure is easier to bundle and margin-protect.
With Huntress, you’re up and running in under 20 minutes—no professional services required, though onboarding support is always available at no charge. The SOC handles triage, investigation, and the bulk of response, so teams of all sizes get real security outcomes without needing a dedicated internal analyst.
Sophos MDR offers comparable SOC capabilities, but the broader ecosystem skews more enterprise. More products to manage, more decisions to make on configuration, and a tiered structure that can push SMBs toward higher-commitment purchases to get the coverage level they actually need.
Yes. The Huntress Managed Security Platform brings endpoint detection and response, identity threat detection, SIEM, and security awareness training into a single console, backed by one SOC and one pricing model.
With Sophos, full cross-layer coverage often means managing separate SKUs and portals for Intercept X, MDR, server coverage, and other integrations. Huntress lets you consolidate those outcomes—and keep or phase out Sophos components where they still make sense—without weakening your security posture or multiplying the number of platforms your team has to work in every day.