What is IOA in Cybersecurity? A Proactive Approach to Threat Detection
Written by: Brenda Buckman
Published: 9/19/2025



FAQ
IOA = Spotting trouble as it unfolds. It’s like noticing someone jiggling your front door handle.
IOC = Evidence discovered after the fact. This is like finding muddy footprints in your house.
IOAs focus on attacker behaviors, like privilege escalation or lateral movement, while IOCs are built around clues left behind, including file hashes or suspicious IP addresses. Bottom line? IOAs give you a shot at stopping an attack in real time. IOCs help with the cleanup.
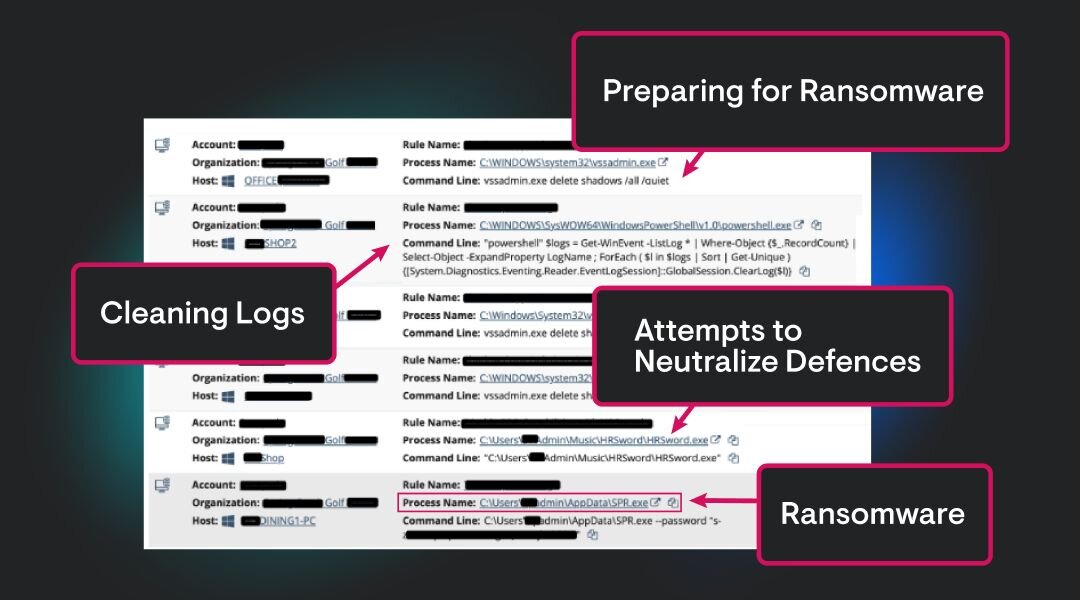
Using PowerShell to switch off antivirus software
Digging into credential stores like LSASS (a.k.a., stealing passwords)
Tweaking registry keys to stay on your system longer
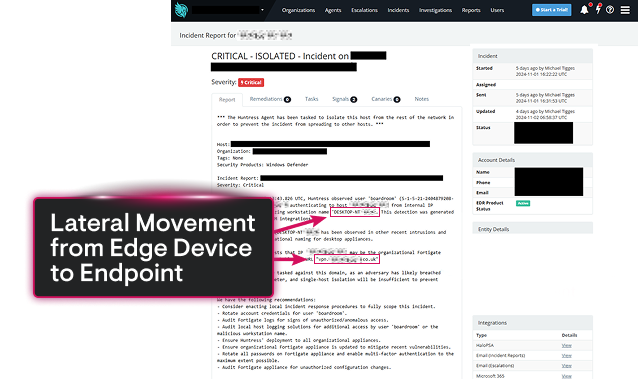
Hopping between systems via RDP or SMB (lateral movement)
Odd parent-child processes (e.g., Excel launching cmd.exe...weird, right?)
These moves reveal attacker intent, even if no malware is caught.