Credential Stuffing



Huntress Managed SAT
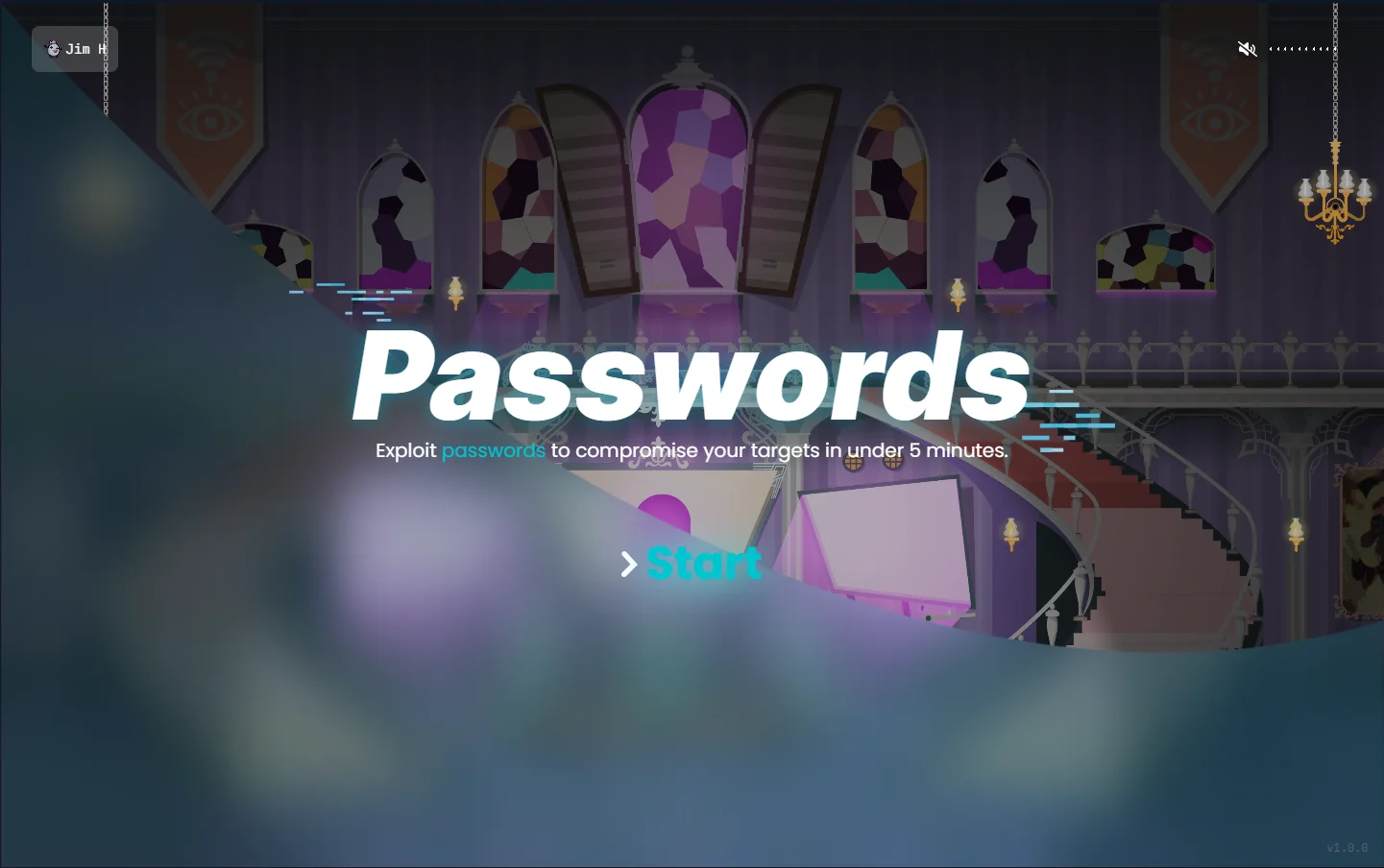
Password Simulation
Credential stuffing works because people reuse passwords. See how Huntress SAT turns that habit into a learning moment—before an attacker exploits it.
FAQs about credential stuffing
Credential stuffing is a type of cyberattack where hackers use stolen login credentials (like usernames and passwords) from a data breach to try and access multiple accounts. They bank on people reusing the same passwords across different services.
Attackers use automated tools, like bots, to test stolen login details across various websites. If a match is found, they gain access to that account. This process is often done at scale, targeting hundreds or thousands of accounts in one go.
Credential stuffing can lead to:
- Unauthorized access to sensitive accounts (banking, email, etc.)
- Identity theft and financial loss
- Business disruptions, including data breaches
- Reputational damage for organizations affected by breaches
Credential stuffing is effective because many people reuse passwords across accounts, making stolen credentials from one breach usable on other platforms. Weak passwords and lack of multi-factor authentication (MFA) make it worse.
Here are some tips:
- Use unique, strong passwords for every account.
- Enable MFA for added security.
- Avoid reusing passwords.
- Leverage a password manager to generate and store secure passwords.
Businesses can use:
- Web application firewalls (WAFs) to detect and block malicious bots
- MFA to add an extra layer of security
- Login anomaly detection systems to monitor suspicious activity
No. While both involve guessing passwords, credential stuffing uses already stolen credentials, whereas brute force attacks systematically guess character combinations to crack passwords.