NFS Security: What It Is, How Attackers Exploit It, and How to Defend Against It
Written by: Lizzie Danielson
Last Updated: 2/17/2026



Frequently asked questions about NFS security
In cybersecurity, NFS (Network File System) is a protocol and common attack surface. Attackers target NFS because misconfigured exports can provide unauthenticated access to sensitive files, a mechanism for privilege escalation via root squashing misconfigurations, and an avenue for lateral movement within a network. NFS security focuses on hardening export configurations, enforcing strong authentication, and monitoring for unauthorized access.
NFS uses port 2049 (TCP and UDP) for file system operations, and port 111 (TCP and UDP) for the RPC portmapper service that NFS depends on. Both ports should be restricted at the firewall to only allow connections from trusted hosts.
NFS is not encrypted by default in NFSv2 and NFSv3. All data is transmitted in plaintext, making it susceptible to network interception. NFSv4 supports encryption when configured with Kerberos in krb5p mode, which provides authentication, integrity checking, and full encryption of data in transit.
Root squashing is an NFS security feature that maps the root user on a client machine (UID 0) to an unprivileged anonymous user on the NFS server. This prevents a remote user with root access from automatically having root-level control over files on the server. Root squashing is enabled with the root_squash option in /etc/exports and should be enabled on all NFS exports. Disabling it with no_root_squash creates a significant privilege escalation vulnerability.
NFSv3 relies on IP address and hostname-based trust for access control, has no native encryption, and is vulnerable to UID spoofing. NFSv4 introduces support for Kerberos-based authentication, adds encryption capabilities (krb5p), has better support for access control lists (ACLs), and operates over a single port (2049), simplifying firewall rules. NFSv4 is significantly more secure than NFSv3 when properly configured with Kerberos.
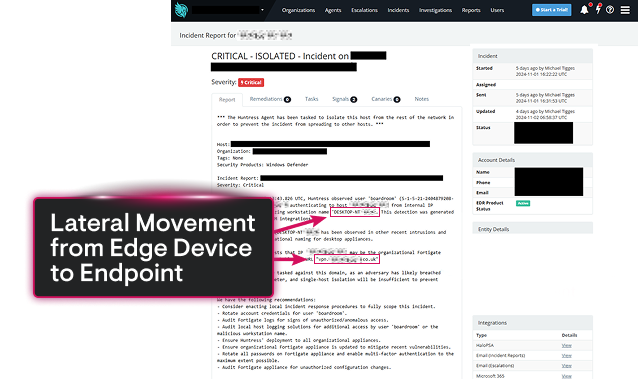
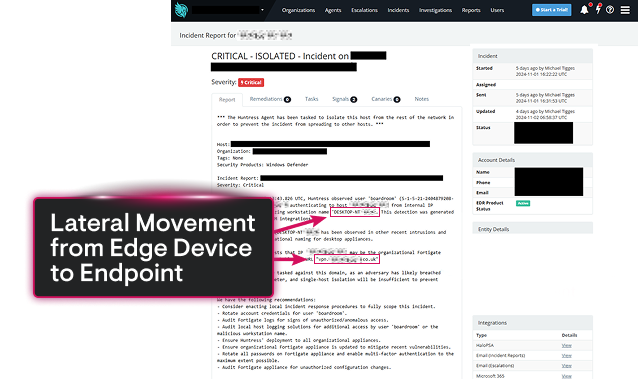
Yes. NFS is a documented lateral movement vector. Attackers who gain access to an NFS share can use it to move files and tools between systems, access credentials that enable further compromise, and in some cases directly pivot to other hosts. MITRE ATT&CK documents NFS-related techniques under T1135 (Network Share Discovery), T1039 (Data from Network Shared Drive), and T1570 (Lateral Tool Transfer).
showmount -e [hostname] is a legitimate Linux command that lists the NFS exports available on a server. It's dangerous from a security perspective because it requires no authentication — any host that can reach port 111 of an NFS server can run showmount and enumerate all available shares. Attackers routinely use this command during reconnaissance to identify accessible NFS shares. You can restrict showmount access by blocking port 111 or disabling the rpcbind service where it isn't needed.
Attackers find exposed NFS shares through internal network scanning with tools like nmap (targeting ports 111 and 2049), running showmount -e against discovered hosts, and using internet scanning tools like Shodan to find internet-facing NFS servers. Many organizations inadvertently expose NFS to the internet through misconfigured firewall rules or cloud security groups.
NFS exploitation has appeared in numerous real-world attacks and penetration tests. Common scenarios include attackers gaining initial access to a corporate network and finding NFS shares containing SSH private keys used to compromise additional servers, and red team engagements where exposed NFS shares containing configuration files with database credentials led to full environment compromise. NFS exploitation is also a standard technique in CTF (Capture the Flag) challenges, reflecting its prevalence as a real attack vector.




Related NFS Topics

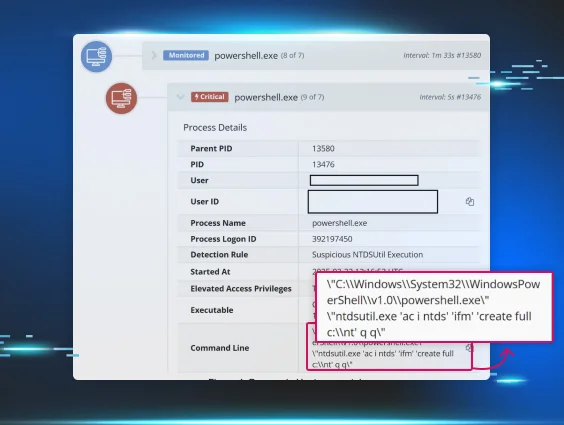
Credential theft is how attackers turn a foothold into full access. This primer covers the techniques, the tools, and the path from initial access all the way to lateral movement.









