What is a Stager in Cybersecurity?
Published: June 4, 2025
Written by: Lizzie Danielson
A stager is a small piece of malicious software that attackers use to start a larger cyberattack. Think of it as a cybercriminal’s “knock on the door”—it’s not the main threat, but it opens the way for more dangerous malware to follow.





How a stager works
Attackers deliver stagers in several ways, usually through phishing emails, malicious websites, or by taking advantage of software flaws. Once the stager lands on a device, it does three main things:
-
Connects to the attacker’s remote server
-
Downloads a bigger, more powerful piece of malware (called the payload)
-
Runs the payload to give the attacker greater control
Splitting the attack into steps helps cybercriminals hide what they’re doing, making it tougher for security tools to spot all the bad activity right away.
Why threat actors use stagers
Stagers are popular for some good (bad) reasons:
-
Stealth: Small bits of code slip past many security tools unnoticed
-
Flexibility: Attackers can choose which payload to deliver after the stager is on your system
-
Bypassing detection: Multi-stage attacks trick antivirus and monitoring systems
The role of command-and-control servers
Once the stager is running, it connects to a Command-and-Control (C2) server controlled by the attacker. Through this connection, the attacker can:
-
Send the main payload
-
Push updates or new commands
-
Pull stolen information from the infected device
Essentially, your system can become one small piece of a much larger criminal network.
Examples of malware that use stagers
Stagers show up in many advanced attacks and well-known tools, such as:
-
Meterpreter (seen in Metasploit)
-
Cobalt Strike
-
Remote Access Trojans (RATs)
-
Advanced Persistent Threat (APT) toolkits
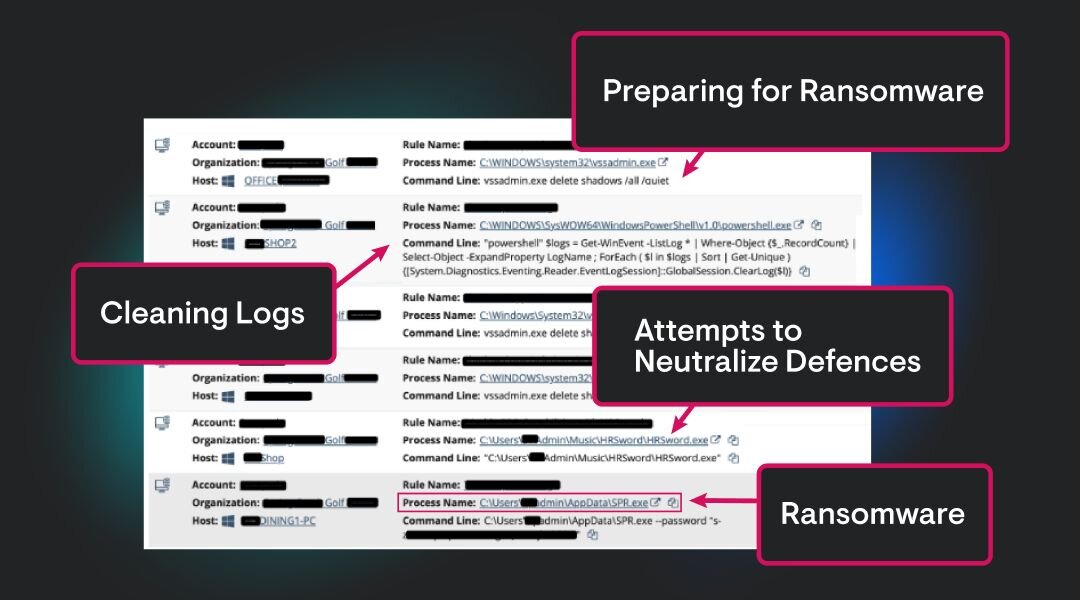
Red teams use them for simulations, but attackers use them to cause real harm too. Read more about proliferating RATS, evolving ransomware threats, and other findings in the Huntress 2025 Cyber Threat Report.
How to defend against stagers
Nobody’s immune, but solid cyber hygiene makes a big difference:
-
Install and update antivirus software. Look for tools that analyze the behavior of files, not just their names or signatures.
-
Patch your operating system and apps as soon as updates are available.
-
Be careful with email attachments and suspicious links—even if they seem to come from trusted contacts.
-
Watch for strange outbound traffic, especially connections to unknown servers.
Closing thoughts
Stagers are just the beginning of bigger attacks. By keeping an eye out for these early warning signs, you’ll make it much harder for cybercriminals to get a foothold in your systems.

Additional Resources
- Read more about What Is a Scam Likely Call and How to Stop ThemLearn what scam likely calls are, how to identify them, and ways to prevent potential scams. Take these steps to protect yourself and your data today.
- Read more about What is Mac Flooding? | HuntressWhat is MAC Flooding?What is Mac Flooding? | HuntressWhat is MAC Flooding?Learn what MAC flooding is, how attackers exploit it to overwhelm network switches, and the steps you can take to detect and prevent this network security threat.
- Read more about What is Zombie Botnet and How to Prevent ItWhat is Zombie Botnet and How to Prevent ItUncover what zombie botnets are, how they work, and steps you can take to detect and prevent these cybersecurity threats with expert tips.
- Read more about What Is Token Theft? How to Protect Your IdentityWhat Is Token Theft? How to Protect Your IdentityLearn about token theft, how attackers exploit stolen authentication tokens, and actionable steps to protect your accounts and systems.
- Read more about What Are TTPs? Cybersecurity Tactics ExplainedWhat Are TTPs? Cybersecurity Tactics ExplainedLearn about TTPs (Tactics, Techniques, and Procedures) in cybersecurity. Understand their role in threat detection and defense strategies.
- Read more about What is a Drive-By Download Attack? | Huntress Cybersecurity 101What is a Drive-By Download Attack? | Huntress Cybersecurity 101Learn about drive-by download attacks, a sneaky cybersecurity threat where malware is downloaded to your device without your knowledge.
- Read more about What is Anti-Spyware & How Does It Protect Your Devices?What is Anti-Spyware & How Does It Protect Your Devices?Learn what anti-spyware is, how it works, and its role in cybersecurity. Uncover steps to protect your devices and data effectively.
- Read more about What Is a Text Bomb? How to Protect Your PhoneWhat Is a Text Bomb? How to Protect Your PhoneLearn what a text bomb is, how text bombing happens, the risks, and what you can do to protect your phone from cyber harassment.
- Read more about What is a RAM Scraper? Cybersecurity 101What is a RAM Scraper? Cybersecurity 101Learn about RAM scrapers, how they work, and the risks they pose. Protect your business from this point-of-sale malware with clear insights and tips.