One incident. No gap.
Last week, something happened in a customer environment that neatly captures where identity security is headed. And where it’s been falling short.
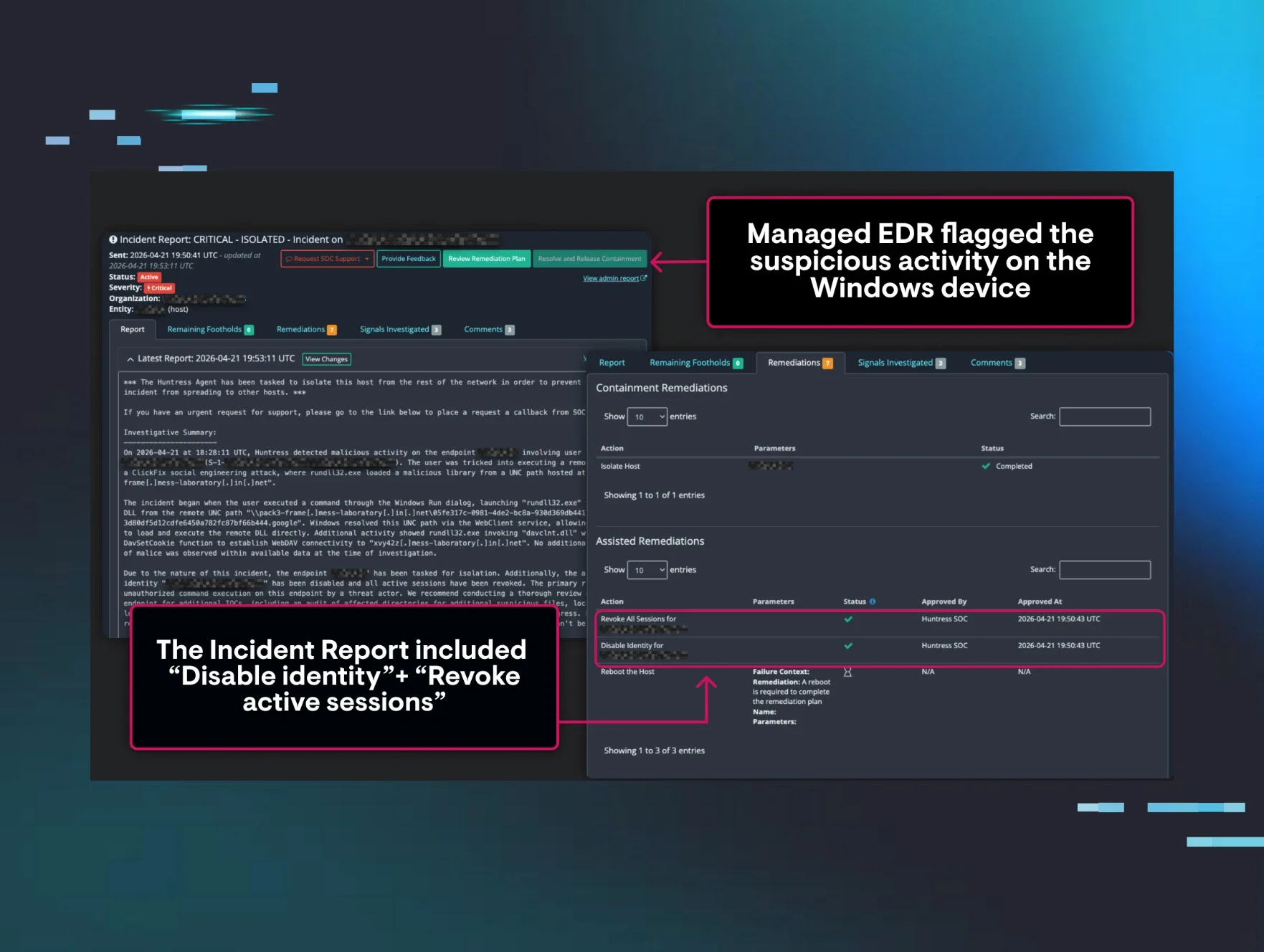
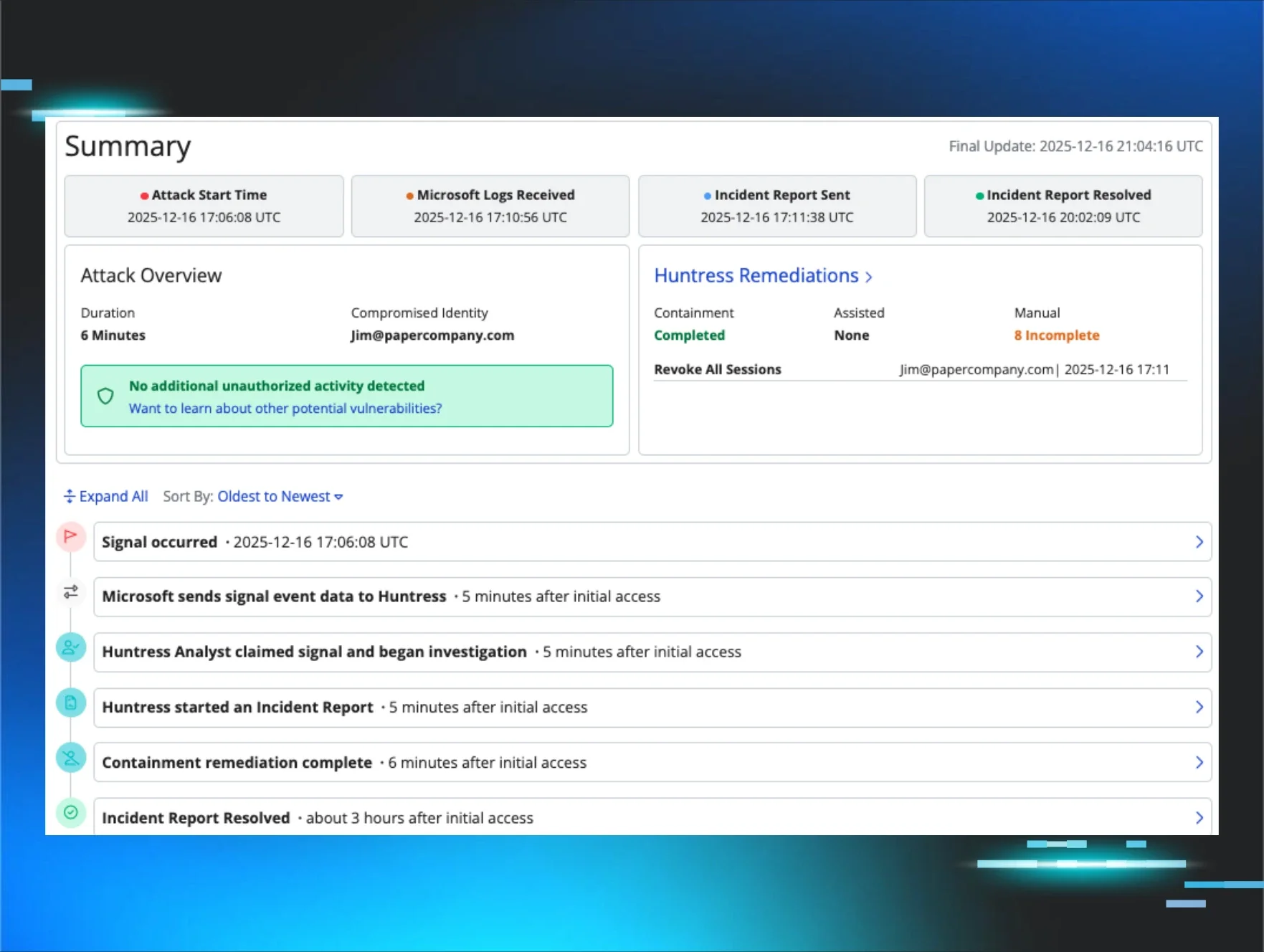
An endpoint was hit with infostealer-style activity. Huntress Managed EDR did exactly what you’d expect: it detected the malicious behavior on the Windows device and raised an Incident Report. But instead of stopping there—isolating the host, killing the process, and calling it a day—the response went further.
In the same motion, the platform mapped the compromised machine to the cloud identity that had been logged into it. The Incident Report didn’t just say “malware found.” It included identity-level actions: Disable identity. Revoke active sessions.
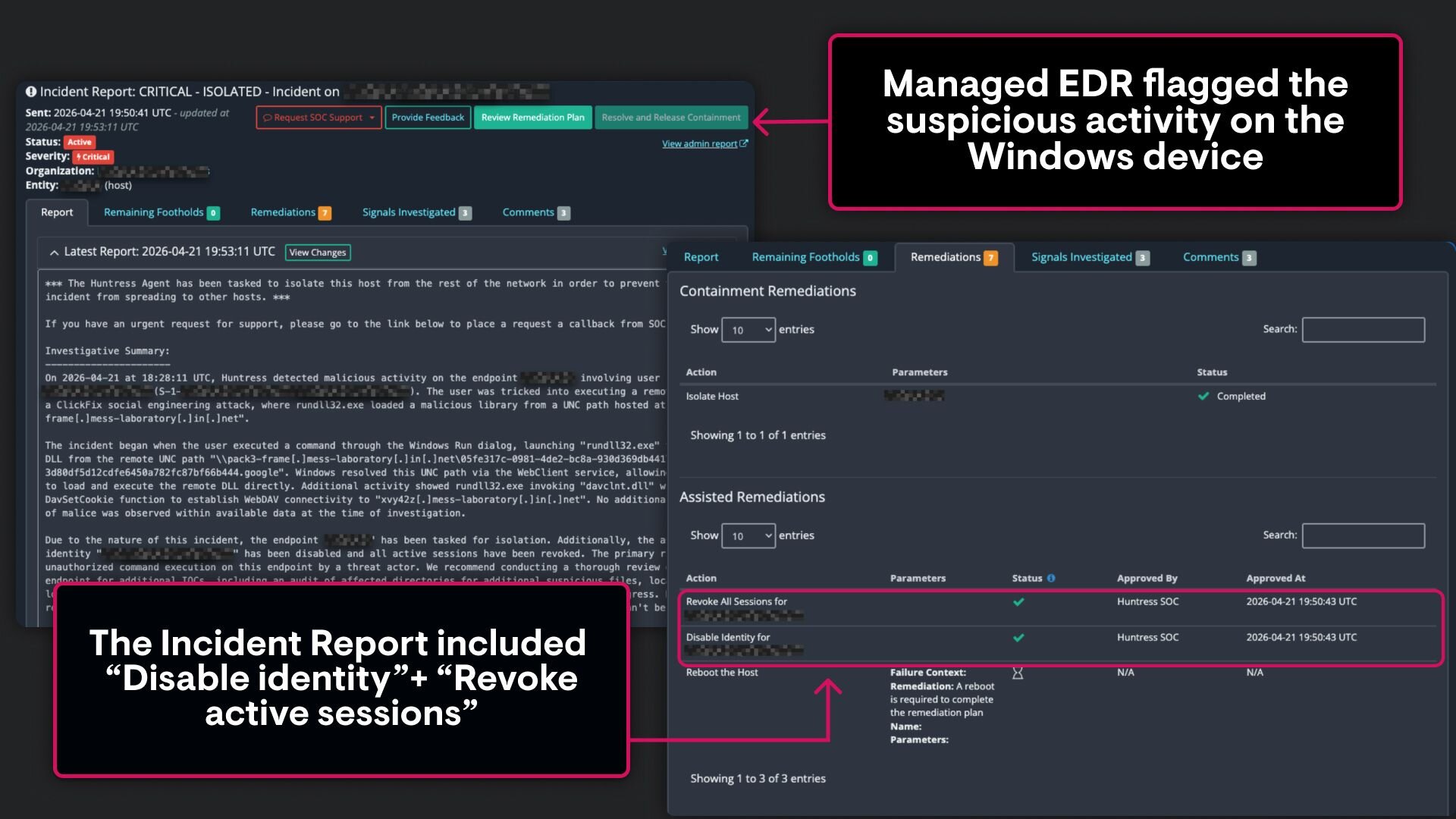
The endpoint was contained. The account was locked down. And it all happened before those stolen credentials could be reused—before they showed up in logs, before they were tested against other services, before they became someone else’s problem.
Even more telling, this all happened before Microsoft had fully delivered the relevant audit logs.
That’s the difference between reacting to identity abuse and getting ahead of it.
Infostealers: Quiet, scalable, and expensive
Infostealers are the reason this matters so much right now. They’ve quietly become one of the most effective (and most underestimated) attack vectors in modern environments. They’re not flashy. And they’re not loud. They’re just relentlessly efficient.
They don’t need to break in. They don’t need to exploit zero-days or chain together complicated techniques. They land on a machine—through phishing, downloads, or commodity malware— and start harvesting. Browser-stored credentials, session tokens, cookies, autofill data. Everything that turns identity into access.
And access, in today’s environments, is everything.
What makes infostealers particularly dangerous isn’t just what they collect, but how quickly that data becomes actionable. Stolen credentials are packaged, sold, replayed, and reused at scale. Sometimes within minutes. And sometimes, before defenders even know there was an initial compromise.
That lag—between compromise and detection, between exposure and response—is where the damage happens. Business email compromise (BEC). Data exfiltration. Lateral movement across SaaS apps. Persistent access through OAuth abuse or inbox rules. The playbook is well understood at this point, and it doesn’t rely on breaking anything. It relies on logging in.
Which is why stopping at the endpoint has quietly become insufficient.
Where traditional response breaks down
Traditionally, this is how these incidents unfold.
EDR detects malware on a machine. The security team investigates, contains the host, and starts asking the next set of questions. Which users were logged into that system? Were credentials exposed? Should we reset passwords? Revoke sessions? Disable accounts?
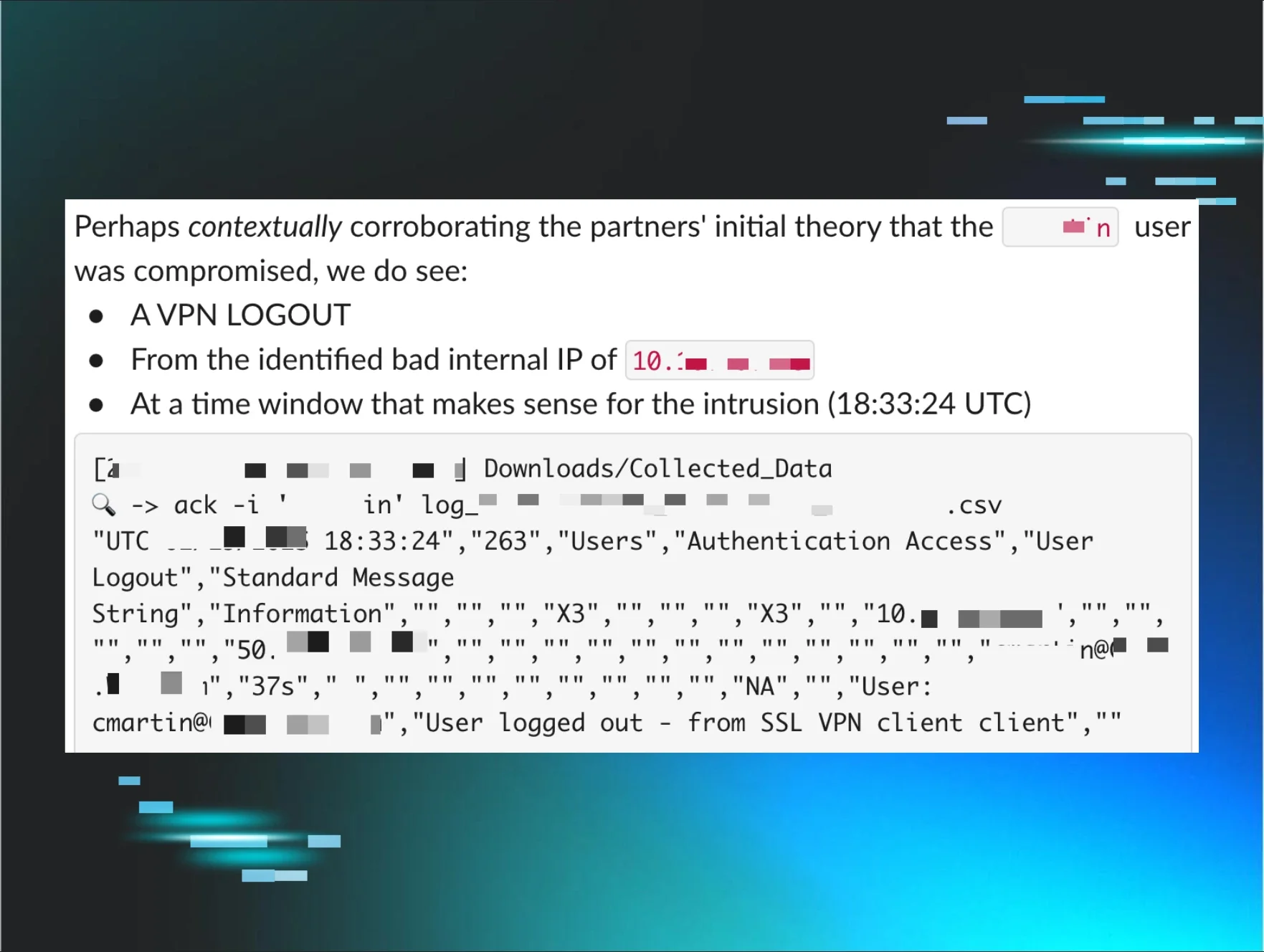
Those answers don’t live in the endpoint. They live in identity systems, like Microsoft 365, Entra ID, and beyond. So the team pivots. They dig through logs, correlate timestamps, and make educated guesses. Sometimes they get it right. Sometimes they overcorrect and disrupt users unnecessarily. Sometimes they miss an account entirely.
Meanwhile, the attacker isn’t waiting for that analysis to finish. They’re already using what they took.
This is the gap. And it’s been accepted as part of the process for far too long.
Closing the gap with EDR/ITDR Correlations
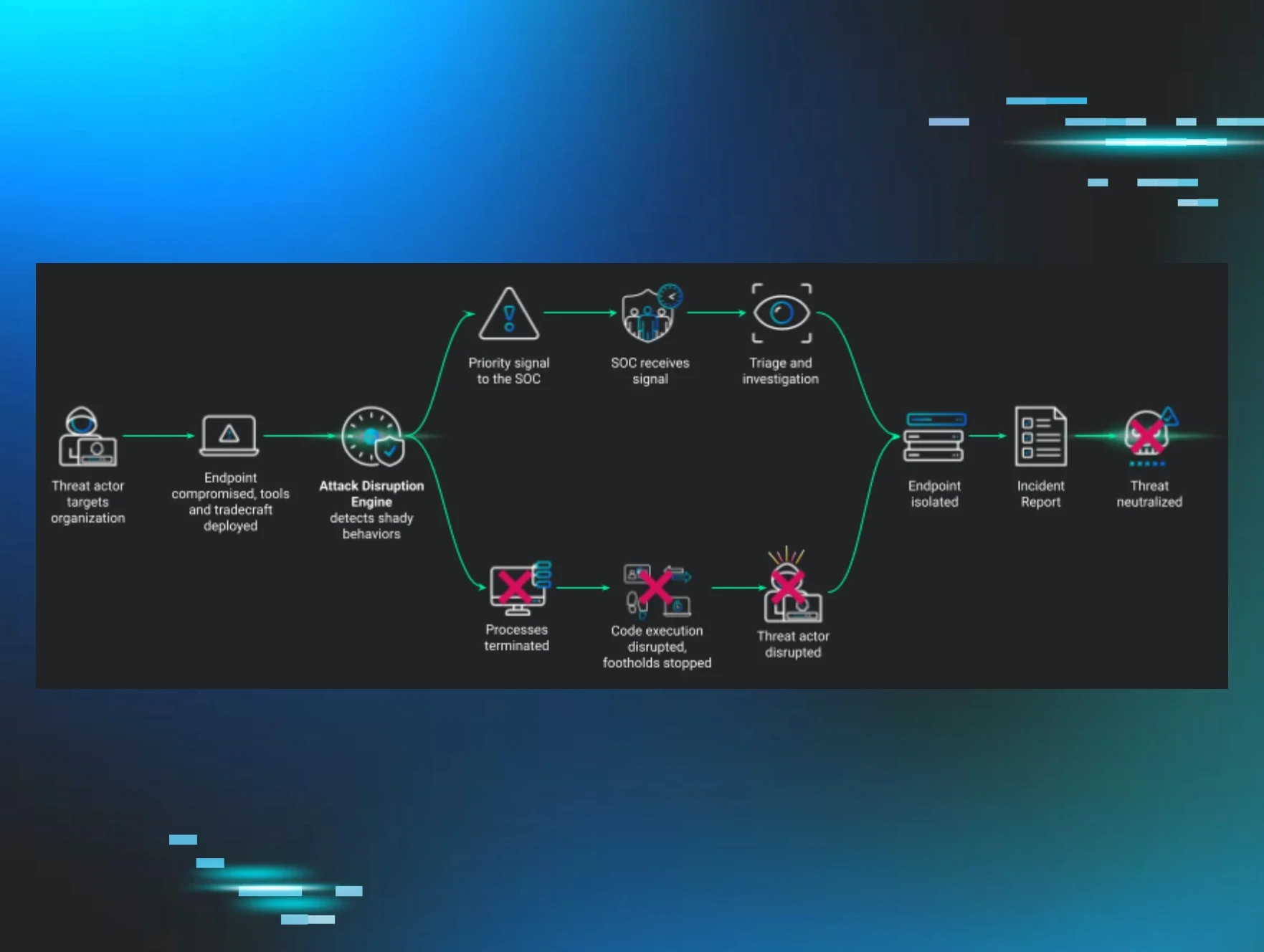
EDR/ITDR Correlations were built to eliminate that gap.
When Huntress Managed EDR detects an attack, like an infostealer, on a Windows endpoint, the platform automatically resolves that compromised machine to the Microsoft 365 cloud identities that were logged in on it. That context isn’t surfaced hours later in a separate tool or buried in logs. It appears directly inside the EDR Incident Report, alongside the endpoint findings.
From there, Managed ITDR does what it’s designed to do: it enables immediate, guided remediation of those identities. Revoke sessions. Disable accounts. Contain the blast radius before stolen credentials can be used.
The result is straightforward, but powerful. You move from:
“We found malware on a laptop,” to “We found the attack, identified the exposed accounts, and locked them down.”
In one flow. One report. One coordinated response.
And, since release, we've stopped 64 of these incidents—with zero false positives!
How it works (without the wait)
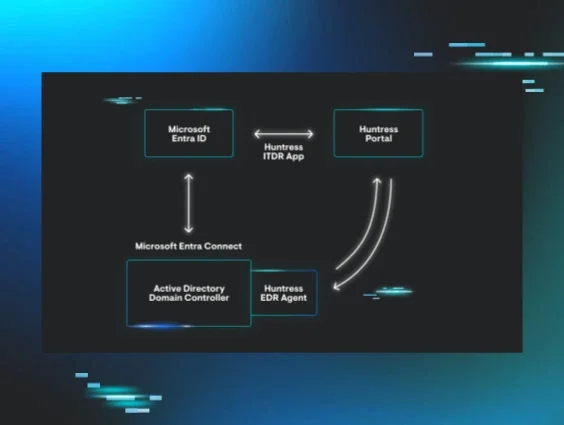
Under the hood, this works because the endpoint already knows more than we’ve historically given it credit for. The Huntress EDR agent continuously collects identity context from the systems it protects—information about which users are logging in, which sessions are active, and how those identities interact with the device.
As detections come in, the platform evaluates that data in real time, resolving potential matches between endpoint activity and cloud identities. When a match is confirmed, those identities are surfaced immediately, and ITDR remediation actions are made available without requiring additional investigation.
Crucially, this approach bypasses one of the biggest bottlenecks in identity security: log latency. Rather than waiting for audit logs to be generated, ingested, normalized, and analyzed, EDR/ITDR Correlations use direct endpoint evidence to infer identity risk almost instantly.
In practice, that means you’re often acting on identity exposure before traditional identity signals even exist.
Why this approach is different
It’s worth pausing here, because this is where a lot of solutions claim overlap.
EDR tools can tell you a machine is compromised. That’s table stakes.
ITDR tools can detect suspicious logins or anomalous behavior in identity systems. That’s valuable, but inherently reactive, because it depends on attacker activity showing up in logs.
XDR platforms promise correlation across domains, but they rely on data pipelines that introduce delay and complexity. By the time the dots are connected, the attacker has often already moved.
EDR/ITDR Correlations take a different approach. They start from the assumption that endpoint compromise and identity exposure are part of the same event, not separate problems to be stitched together later.
That shift matters because it collapses the timeline. It removes guesswork. And it turns what used to be a multi-step investigation into a single, outcome-focused response.
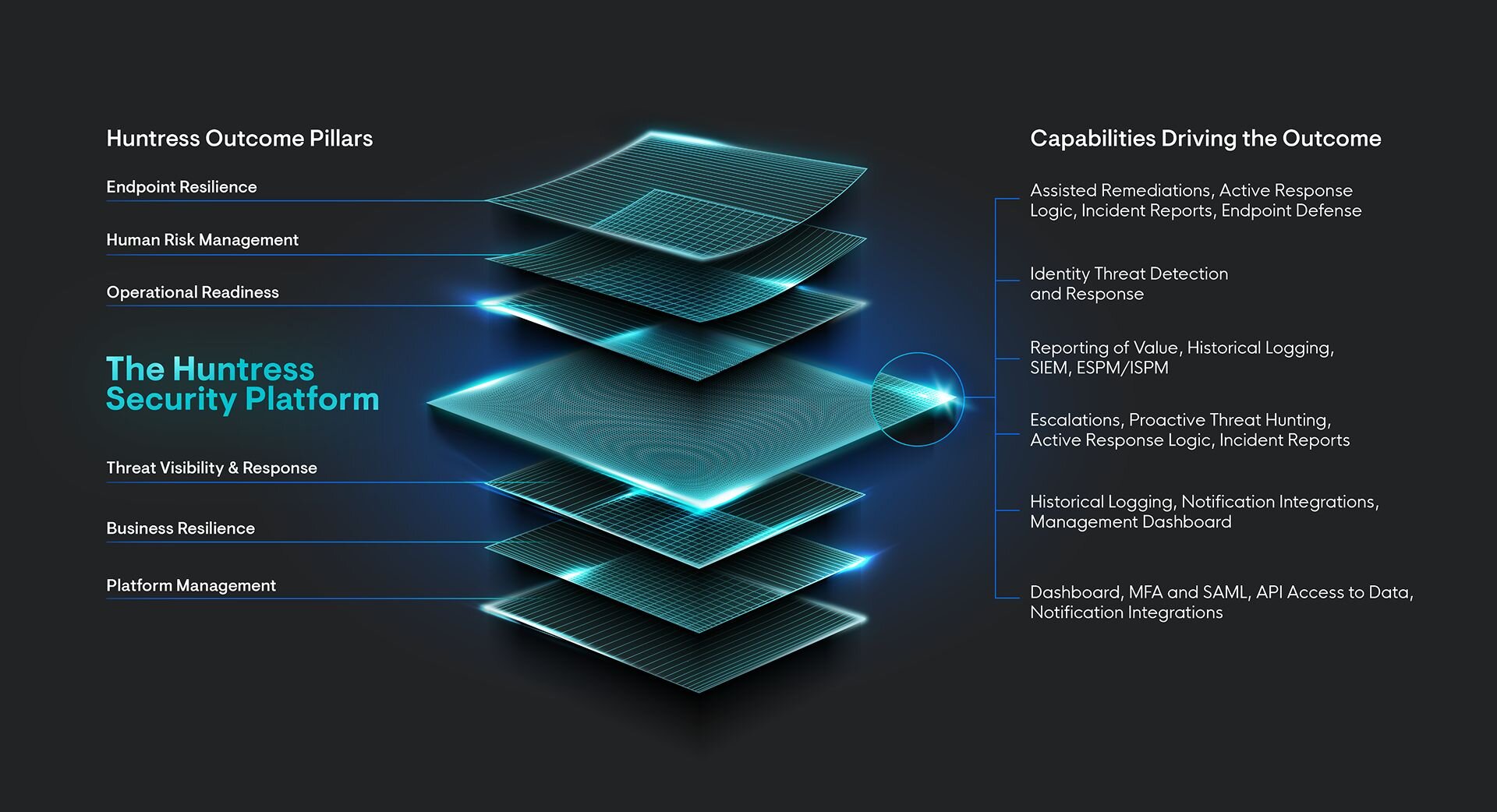
This is what a platform actually does
“Platform” is one of those words that gets thrown around a lot.
Usually, it means a bunch of tools that kind of integrate…if you configure them correctly…and have time to maintain them.
That’s not what this is.
This is a true cross-product capability, built from the ground up to operate as one system. EDR isn’t just feeding alerts into ITDR. ITDR isn’t just enriching EDR.
They’re working together, natively, to produce a single outcome: to stop the attack. Completely.
That’s the idea behind the Huntress Agentic Security Platform. Not more alerts. Not more dashboards. Outcomes.
Speed changes everything
The most tangible difference here is speed. Not just detection speed, but speed to meaningful action.
With EDR/ITDR Correlations, multiple steps collapse into one continuous motion: detect the malware, identify exposed identities, and initiate remediation. It’s all driven from a single event.
In real-world scenarios, that means stopping identity abuse before it starts, or at least before it spreads beyond the initial foothold.
For defenders, that shift is hard to overstate.
From fragmented tools to coordinated response
Most teams today are still operating across fragmented tools. One for endpoints. One for identity. Maybe another for logs. When something goes wrong, they become the integration layer, stitching together context under pressure while attackers move faster than the process allows.
With EDR and ITDR working together natively, that burden disappears. The context is already correlated. The actions are already aligned. The response is faster, cleaner, and far more consistent.
Attackers move seamlessly from endpoint to identity. Your defenses should too.
Closing the gap for good
EDR/ITDR Correlations are rolling out to organizations running both Huntress Managed EDR and Managed ITDR. They’re not add-ons or bolt-on features; they’re core capabilities that reflect how modern detection and response should work.
That gap between endpoint compromise and identity protection has been tolerated for too long.
Now it’s closed. And once you operate without it, there’s no going back.
👉 Interested in seeing EDR/ITDR Correlations in action? Sign up for a free Managed EDR and Managed ITDR trial today!