For a long time, most organizations treated Google Workspace (GWS) like a productivity tool.
Email. Documents. Calendars. Chat. Useful, sure. But not exactly the thing keeping security teams awake at night.
Attackers see it differently.
To them, GWS isn’t just collaboration software. It’s identity infrastructure. The connective tissue of modern business. And once you start looking at it that way, the risk picture changes pretty quickly.
Think about it.
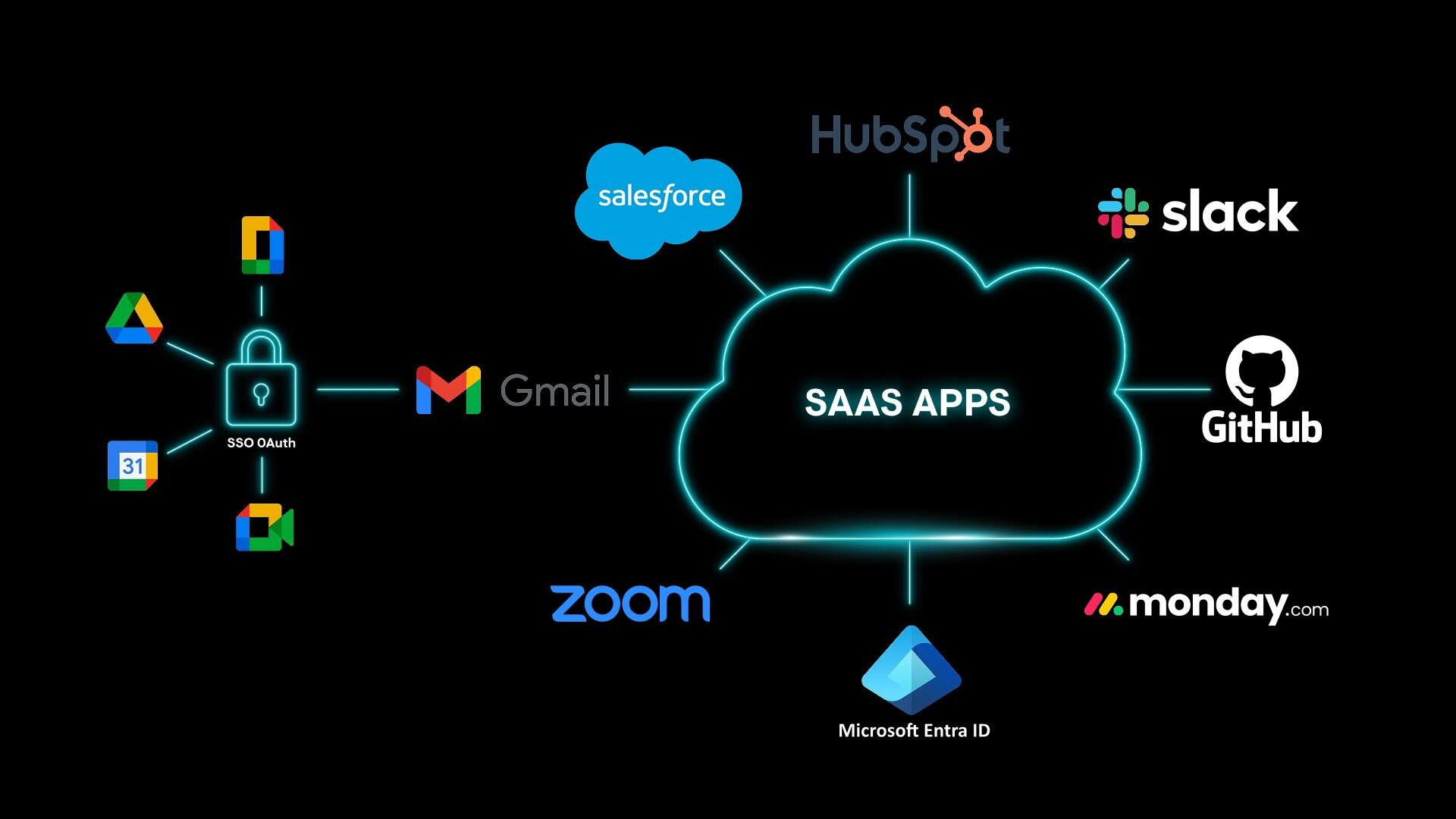
A compromised Workspace account doesn’t just expose email. It opens doors to password resets across SaaS platforms, MFA verification messages, OAuth permissions, vendor conversations, financial workflows, and internal trust relationships. Gmail, in many environments, quietly functions as the root identity layer for the cloud.
Which means that when attackers gain access to a Workspace account, they rarely stop at the inbox. They pivot. They expand. They start treating that identity like a launchpad.
That’s exactly why we’re introducing Huntress Managed Identity Threat Detection and Response (ITDR) for Google Workspace—bringing the same SOC-led identity protection we deliver for Microsoft 365 to the Workspace ecosystem.
And we’re not starting from scratch here.
Huntress Managed ITDR already protects over 10 million identities across environments, with a 3-minute mean time to respond, and a false positive rate under 5%. It’s battle-tested, not theoretical.
This expansion simply brings that same proven approach to Google Workspace.
Because attackers aren’t breaking in anymore. They’re logging in.
Google Workspace has become a very attractive target
GWS adoption has exploded over the past decade. Small businesses run their entire company on it. Mid-market organizations rely on it for identity and collaboration. MSPs manage thousands of tenants.
From an attacker’s perspective? That’s a lot of opportunity.
Over the past two years alone, researchers and incident responders have observed a steady evolution in how threat actors abuse the Workspace ecosystem. The techniques keep changing, but the pattern is consistent: identity first.
Some of the trends we’re seeing include:
-
Business email compromise (BEC) campaigns tied to Gmail account takeovers
-
Phishing delivered through trusted Google services like Drive or Slides
-
OAuth and consent phishing replacing traditional credential theft
-
Identity token theft through SaaS integrations
-
Workspace subdomain abuse triggering legitimate password resets
Here's the tricky part. Most of these attacks don’t involve malware at all. No suspicious attachments. No obvious payloads. No endpoint alerts lighting up dashboards. Just normal activity.
And that’s exactly why it works.
This isn’t a tooling gap as much as it’s a visibility gap. Most security tools weren’t built to detect identity abuse that happens after authentication.
But attackers are living there now. And the data backs it up.
In 2025, 79% of all Huntress critical/high incident reports were identity-related. Not endpoint. Not malware. Identity.
That’s where the fight moved.
Business email compromise isn’t just email anymore
When people hear BEC, they usually picture a phishing email asking for a wire transfer.
That still happens. But the modern playbook is a little more sophisticated. Today’s BEC campaigns often unfold as multi-stage identity attacks. They move slowly. Quietly. Sometimes, surprisingly methodically.
First comes INITIAL ACCESS. Maybe stolen credentials from a phishing kit. Maybe session hijacking. Maybe OAuth abuse. However it happens, the attacker gains access to a Workspace account.
Next comes DISCOVERY. They start reading email conversations, mapping relationships, looking for financial workflows, vendor discussions, approval chains. It’s reconnaissance, but through a mailbox.
Then comes STEALTH. Attackers often create Gmail filter rules designed to delete security notifications or archive responses to malicious emails. The victim never sees warning messages. Replies disappear into the void. Everything looks normal. Which is exactly the point.
After that comes ACTION. Phishing messages. Fraud requests. Internal social engineering. Whatever makes money.
And finally, PERSISTENCE. Forwarding rules. OAuth tokens. Backup access paths. Attackers assume passwords might get reset eventually, so they prepare alternatives.
The important detail here is easy to miss—email compromise isn’t the goal. It’s the starting point.
Once attackers control a Workspace identity, they can pivot into SaaS platforms through password resets, MFA messages, and OAuth workflows. In practice, Gmail becomes a kind of identity clearinghouse—one compromised account unlocking access to many others.
That’s why defending Workspace environments requires something more than spam filtering. It requires identity detection and response.
Introducing Managed ITDR for Google Workspace
Huntress Managed ITDR for GWS focuses on detecting the behaviors attackers can’t easily disguise. Not raw logs. Not endless alerts. Behavior.
And when something suspicious happens, the Huntress SOC investigates and takes action. No waiting around for overwhelmed security teams to triage alerts at 2am.
At launch, the platform focuses on a handful of high-impact attack patterns.
Because stopping a few critical behaviors often shuts down entire attack chains.
Unexpected login activity
Attackers rarely log in from the same place as legitimate users. They prefer VPNs, proxies, or rented cloud infrastructure to obscure their location.
Managed ITDR watches for authentication patterns that don’t fit—risky networks, unusual geographies, or infrastructure commonly abused by threat actors.
When those signals appear, our analysts can quickly revoke sessions and remove attacker access.
Short dwell time. Fewer surprises.
Malicious inbox rules
This one shows up constantly in real-world incidents.
Attackers create Gmail filter rules designed to automatically delete or archive security notifications. MFA alerts disappear. Suspicious login warnings vanish. Victim replies to phishing messages get hidden.
From the outside, the account looks perfectly normal. But inside the inbox? Quiet manipulation.
Managed ITDR detects those rule changes, and Huntress analysts remove them, shutting down one of the most common persistence techniques attackers rely on.
Malicious datacenter infrastructure
Threat actors increasingly route authentication through cloud hosting providers instead of residential networks.
So Managed ITDR tracks login activity tied to datacenter providers and ASNs commonly used in attacks, surfacing suspicious access earlier in the attack chain.
Think of it as a behavioral signal attackers struggle to disguise.
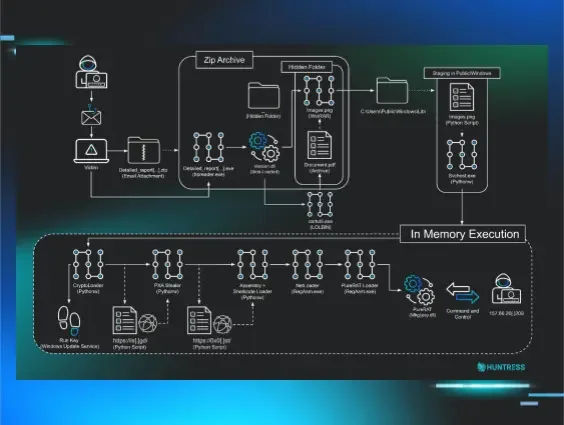
A real Google Workspace identity attack
Let’s make this concrete. Below is a real example of how an identity attack unfolded inside a Workspace environment.
Here’s what happened:
A threat actor compromised a GWS account using stolen credentials. To hide their location, they routed authentication through suspicious datacenter infrastructure and proxy services.
Once inside the account, they got to work.
The attacker created Gmail inbox rules designed to delete Google security alerts - essentially blinding the victim to suspicious login activity. Classic BEC setup.
The next step likely would've been phishing messages or financial fraud requests sent from the trusted account.
But the attack never got that far.
Managed ITDR detected two signals almost immediately: authentication from suspicious infrastructure and newly created inbox rules suppressing security alerts.
The identity compromise was escalated to the Huntress SOC.
Our analysts revoked the attacker’s access, removed the malicious rules, and began investigating related indicators across the environment.
That investigation uncovered additional activity: password change attempts, probes against administrative accounts, and attempts to distribute malicious calendar invites.
Those indicators were then used to pivot across Huntress telemetry, identifying other identities targeted by the same threat actor.
The attack stopped before it escalated. Minimal disruption. Minimal investigation time.And no fraudulent invoices flying around.
This isn’t a new bet for Huntress
This launch isn’t a “maybe this works” moment. It’s an extension of something already working at scale.
Today, Huntress Managed ITDR protects over 93,000 organizations across Microsoft 365 and Google Workspace environments.
We sent over 116,000 positive ITDR incident reports in 2025 alone. And we’re already at more than 34,000 in 2026.
That’s not noise. That’s real attacker activity, investigated and acted on.
Behind the scenes, we’ve continued investing heavily in identity protection, rolling out features like Incident Report Timelines and mass outbound phishing detection to improve both visibility and response.
And it shows.
Turns out, when you solve real problems, people notice.
One identity defense layer for Microsoft and Google
Many organizations operate in hybrid environments today. Microsoft 365 on one side. Google Workspace on the other.
Until recently, protecting those ecosystems meant juggling multiple tools and fragmented workflows.
With the expansion of Managed ITDR to Google Workspace, Huntress now provides:
-
One platform
-
One SOC
-
Identity protection across both ecosystems
Simple idea. Big operational relief.
Identity is the new endpoint
Security changes slowly. Attackers change fast.
Right now, the reality is simple: attackers don’t need malware to cause serious damage. They just need access to the right identity.
And GWS sits right in the middle of modern business operations—powering communication, authentication, and trust relationships across the cloud, making it a very attractive target.
So we expanded Managed ITDR to protect it. Because if attackers are treating identity like the front door to the business…
...someone should be watching that door.
All the time.
And that's the job Huntress shows up for every day.
👉 Interested in protecting your GWS identities? Sign up for a free 14-day trial of Managed ITDR.